Email
Phishing is the attempt to gather personal information using any combination of deceptive messages, links, calls, emails and websites. Phishing emails are typically the most common types of phishing that you will encounter. These deceptive emails tend to impersonate a legitimate person or company in order to obtain information from you.

Our mail system tries to help by automatically blocking or warning you of messages that it detects as malicious, but an email that's disguised really well or from a legitimate account can still navigate through our filters and arrive in your inbox.
It's up to you to read those messages carefully!
Identifying Malicious Emails
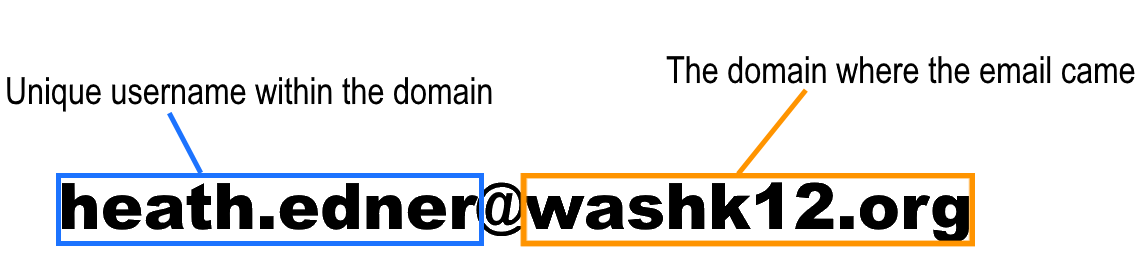
Check the person's full email address. Emails from district personnel will always be from user.name@washk12.org, accounts that impersonate administration would not be from the washk12.org domain.
However, email scammers will try to create domain names that look very similar to legitimate ones, or you may not always know what a legitimate domain name would be for a particular company. Therefore, we have signs to look for in the content of the email you recieved that we can respond to.
Also, keep in mind that a malicious email could still come from a washk12.org account if that account was compromised.
Assessing External Emails
If we are unsure if the email is legitimate or not, we need to ask ourselves two questions: what does this email want from me? and how does it want me to respond? The example below is notifying the recepient of an upcoming charge. They are hoping to confuse and panic the recepient so that they will call the phone number and connect them to the scammer, who will then further impersonate the company.
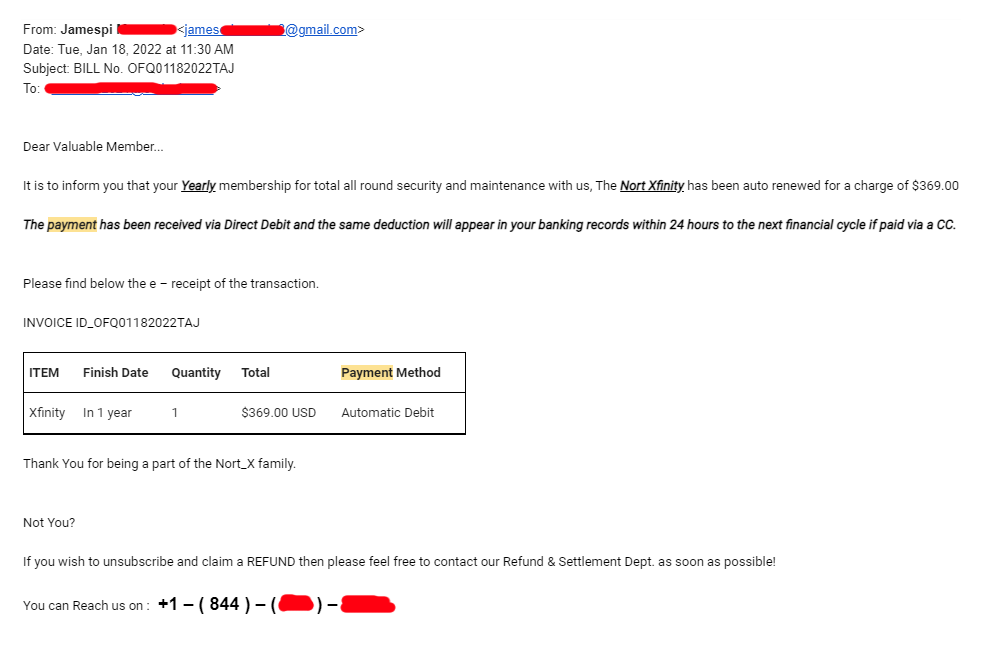
- Check the full email address: This email is coming from a gmail account which a responsible company would not use.
- What does this email want? They want you to believe that this company is charging you an annual fee, inciting a quick response with little time to assess the validity of the email.
- How does it want you to respond? They want you to call their phone number so that they can gather more information, especialy if you're an existing customer for this company so that you can give them account information.
Assessing Internal Emails
Although the email looks like it's from a district employee, we can tell by the content of the message that something is suspicious. This is potentially a district employee whose account has been compromised.
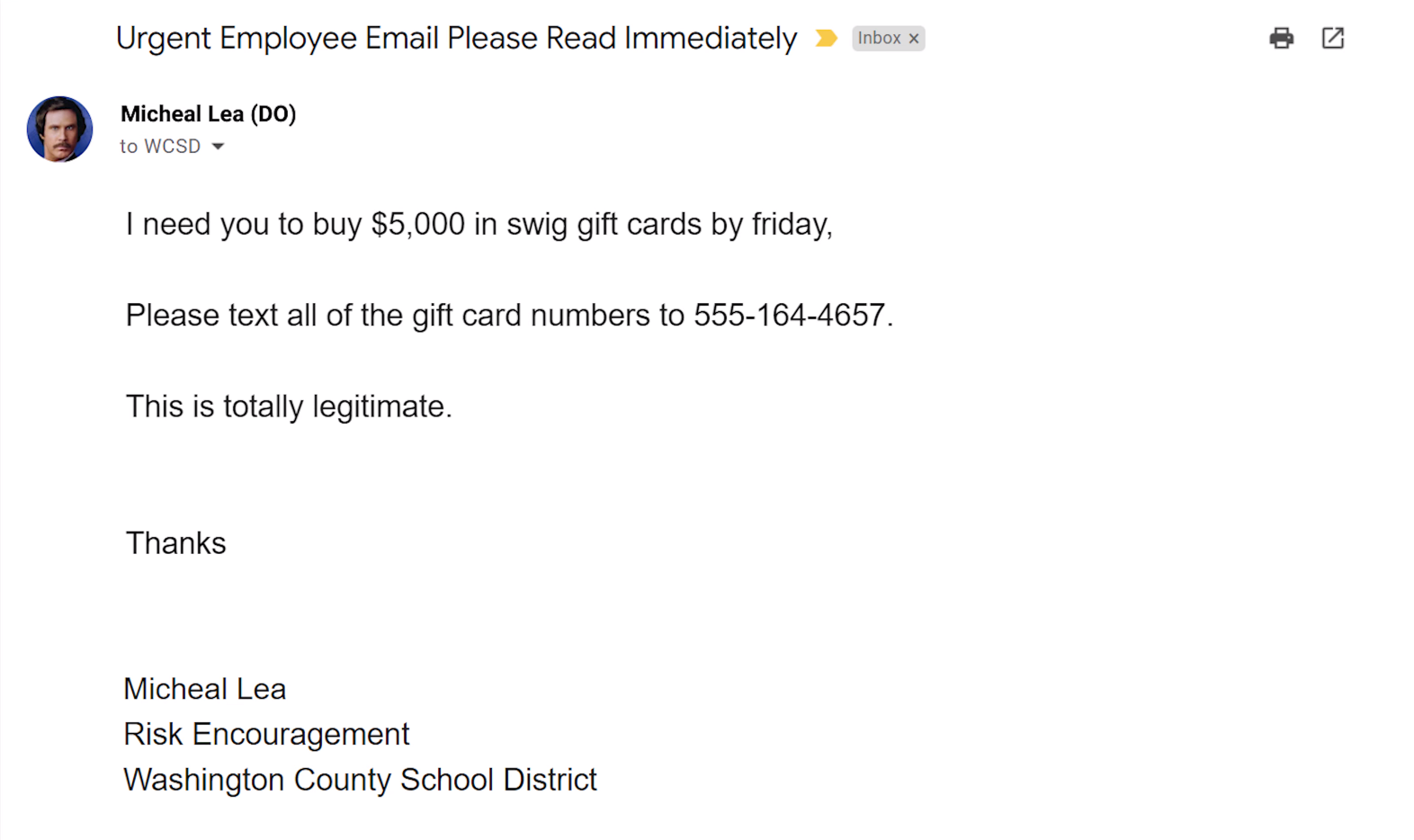
- Check the full email address: This is coming from a legitimate washk12 account but the content of the email gives us cause to think this account is being used by somebody else.
- What does this email want? They want us to purchase something out of the ordinary in addition to violating district policies which this person would NEVER ask you to do...right?
- How does it want you to respond? They want the information gathered (gift cards) to be sent to an unknown location (phone number), again very out of the ordinary.
Notices from Other Companies
Bad actors will take advantage of companies that send emails or other notifications on their behalf, the most common being from Google Drive or PayPal. Since the email is genuinely from another company or service, it's very difficuly to block an incoming malicious email with this method without blocking the company completely.
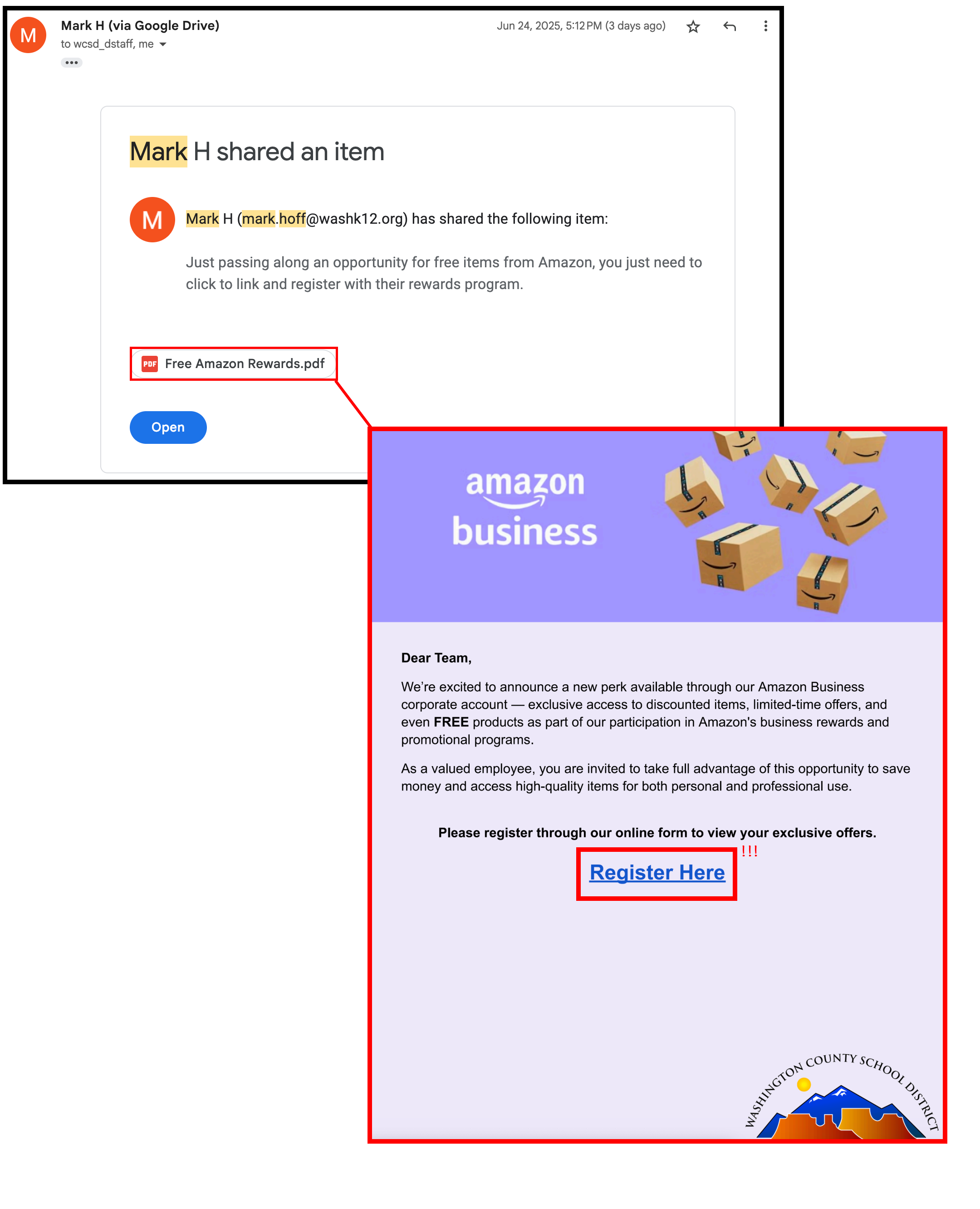
It's very important to apply a similar process that you would use when assessing internal emails.
- Be skeptical of the content: This is coming from a legitimate company, but the content of the email is suspicious and the sender is unknown.
- What does this email want? If it has a link embedded into the shared document, be extremely hesitant. PDF documents are notorious for taking you to a malicious website.
- How does it want you to respond? What information do they want to collect from you and what website is collecting it?
Fake Sign-In Pages
It is very common for a phishing email to lead you into a page impersonating the company in order to collect your account login credentials.
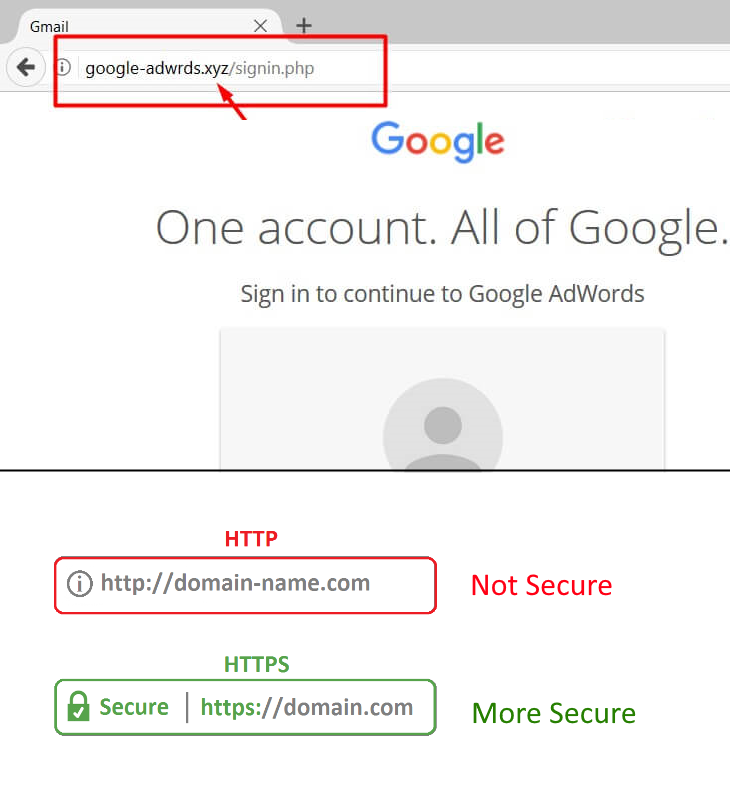
Check the full website address. Similar to checking an email address, a login page should be from a known domain for that company.
It's become a standard for modern websites to use HTTPS. This makes your connection to the site more secure and will show a lock icon in the adddress bar
Seeing the "Secure" Lock icon does not mean the site cannot be malicious, more advanced phishing pages will go through the steps to acquire a lock.
Malicious QR Codes
A QR (Quick Response) code is a type of barcode that moderm smartphones can now easily scan and read through an app or directly built into the camera. QR codes can be used for many different digital purposes such as website links, login methods, and banking transactions.

Security news outlets are steadily reporting occurences of scammers placing QR codes in public places and attempting to con victims into scanning the codes to collect their information.
What can you do? Use QR code payments only in circumstances that you consider normal, don�t be rushed or talked into paying in a way that you are not completely familiar with. Treat a QR code like any other link. Don�t follow it if you don�t know where it originated from, or if you don�t fully trust the source.
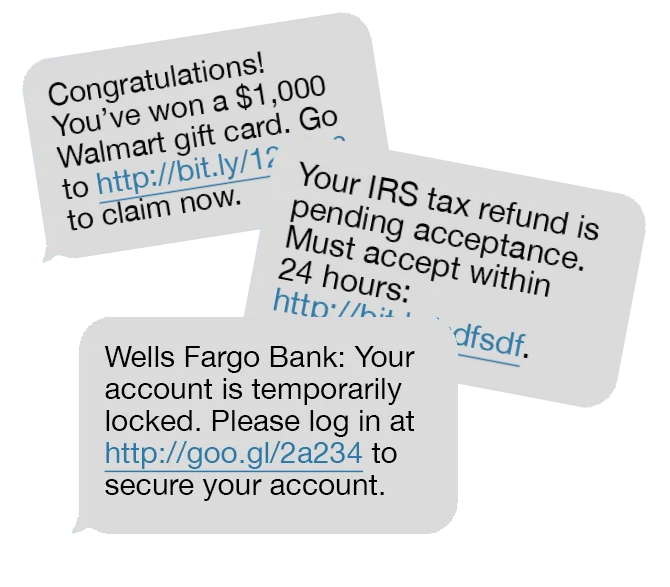
Malicious Text Messages
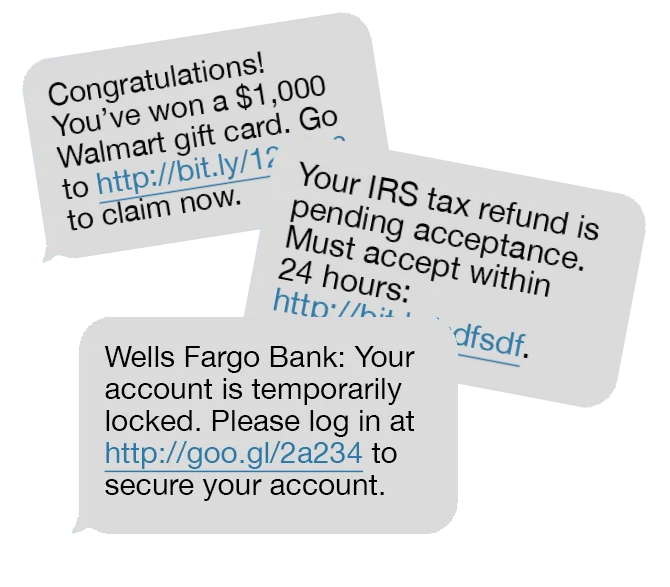
Perhaps even more annoying than spam emails are spam text messages. Ranging from actual conversations with a scammer to automated marketing links, tens of billions of scam messages are sent every year.
- Don't rely on the area code - sophisticated texts or calls will use an area code you may be famaliar with, making you more likely to respond.
- Shortened links can take you anywhere - links in text messages are typically ran through a "shortener" to shorten the length of the link. This subsequently masks the actual address of the link and you won't know where it's going until you click it. Read more about URL shorteners here
- Protect your number - In addition to placing your number on do-not-call-lists, modern phones and phone carriers offer additional ways to block, filter, and screen unknown calls to minimize your contact with scams.
Social Security Scams
The Social Security Administration urges everyone to be on the lookout for fake calls, texts, emails, websites, messages on social media, or letters in the mail regarding your Social Security Information.
- Scammers pretend to be from an agency or organization you know to gain your trust.
- Scammers say there is a problem or a prize and pressure you to act immediately.
- Scammers then tell you to pay in a specific way to fix the "issue".
Visit https://www.ssa.gov/scam/ for more information and to report a Social Security related scam.
Taking Appropriate Actions 
You can forward suspicious emails to phishing@washk12.org
If you recieve any internal emails that are out of the ordinary, you can always check with them in-person!
Thank you for reading to the end!
Additional resources
(YouTube) CompTIA: 11 Tips for fake websites & phishing emails
Phishing is the attempt to gather personal information using any combination of deceptive messages, links, calls, emails and websites. Phishing emails are typically the most common types of phishing that you will encounter. These deceptive emails tend to impersonate a legitimate person or company in order to obtain information from you.

Our mail system tries to help by automatically blocking or warning you of messages that it detects as malicious, but an email that's disguised really well or from a legitimate account can still navigate through our filters and arrive in your inbox.
It's up to you to read those messages carefully!
Check the person's full email address. Emails from district personnel will always be from user.name@washk12.org, accounts that impersonate administration would not be from the washk12.org domain.
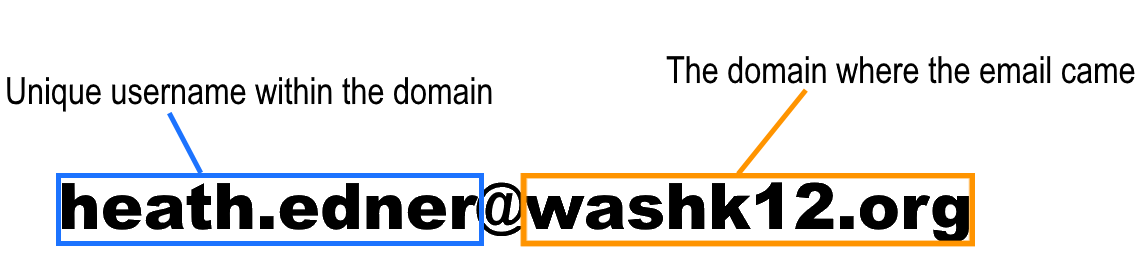
However, email scammers will try to create domain names that look very similar to legitimate ones, or you may not always know what a legitimate domain name would be for a particular company. Therefore, we have signs to look for in the content of the email you recieved that we can respond to.
Also, keep in mind that a malicious email could still come from a washk12.org account if that account was compromised.
If we are unsure if the email is legitimate or not, we need to ask ourselves two questions: what does this email want from me? and how does it want me to respond? The example below is notifying the recepient of an upcoming charge. They are hoping to confuse and panic the recepient so that they will call the phone number and connect them to the scammer, who will then further impersonate the company.
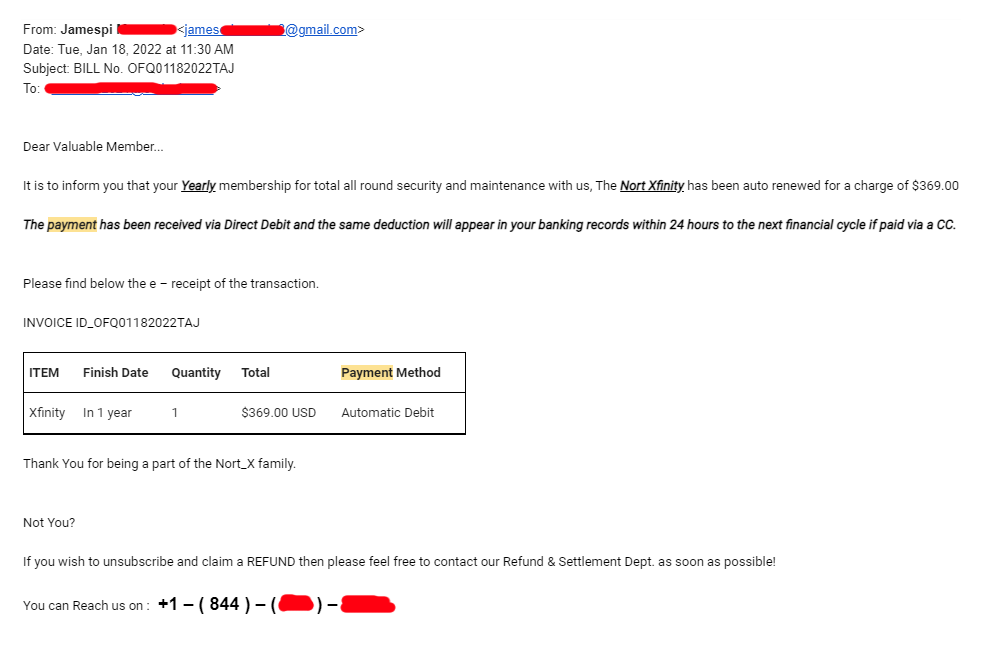
- Check the full email address: This email is coming from a gmail account which a responsible company would not use.
- What does this email want? They want you to believe that this company is charging you an annual fee, inciting a quick response with little time to assess the validity of the email.
- How does it want you to respond? They want you to call their phone number so that they can gather more information, especialy if you're an existing customer for this company so that you can give them account information.
Although the email looks like it's from a district employee, we can tell by the content of the message that something is suspicious. This is potentially a district employee whose account has been compromised.
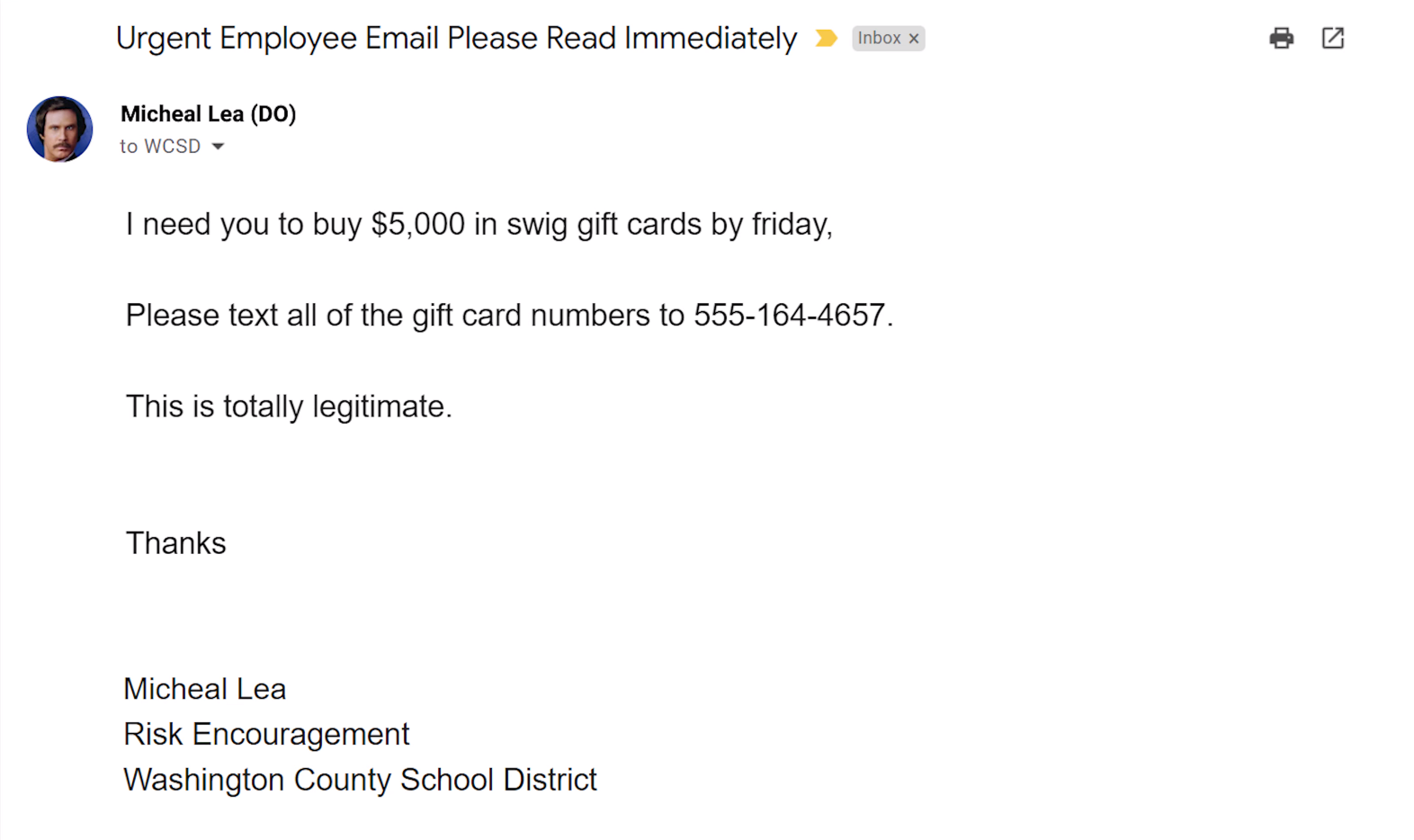
- Check the full email address: This is coming from a legitimate washk12 account but the content of the email gives us cause to think this account is being used by somebody else.
- What does this email want? They want us to purchase something out of the ordinary in addition to violating district policies which this person would NEVER ask you to do...right?
- How does it want you to respond? They want the information gathered (gift cards) to be sent to an unknown location (phone number), again very out of the ordinary.
Bad actors will take advantage of companies that send emails or other notifications on their behalf, the most common being from Google Drive or PayPal. Since the email is genuinely from another company or service, it's very difficuly to block an incoming malicious email with this method without blocking the company completely.
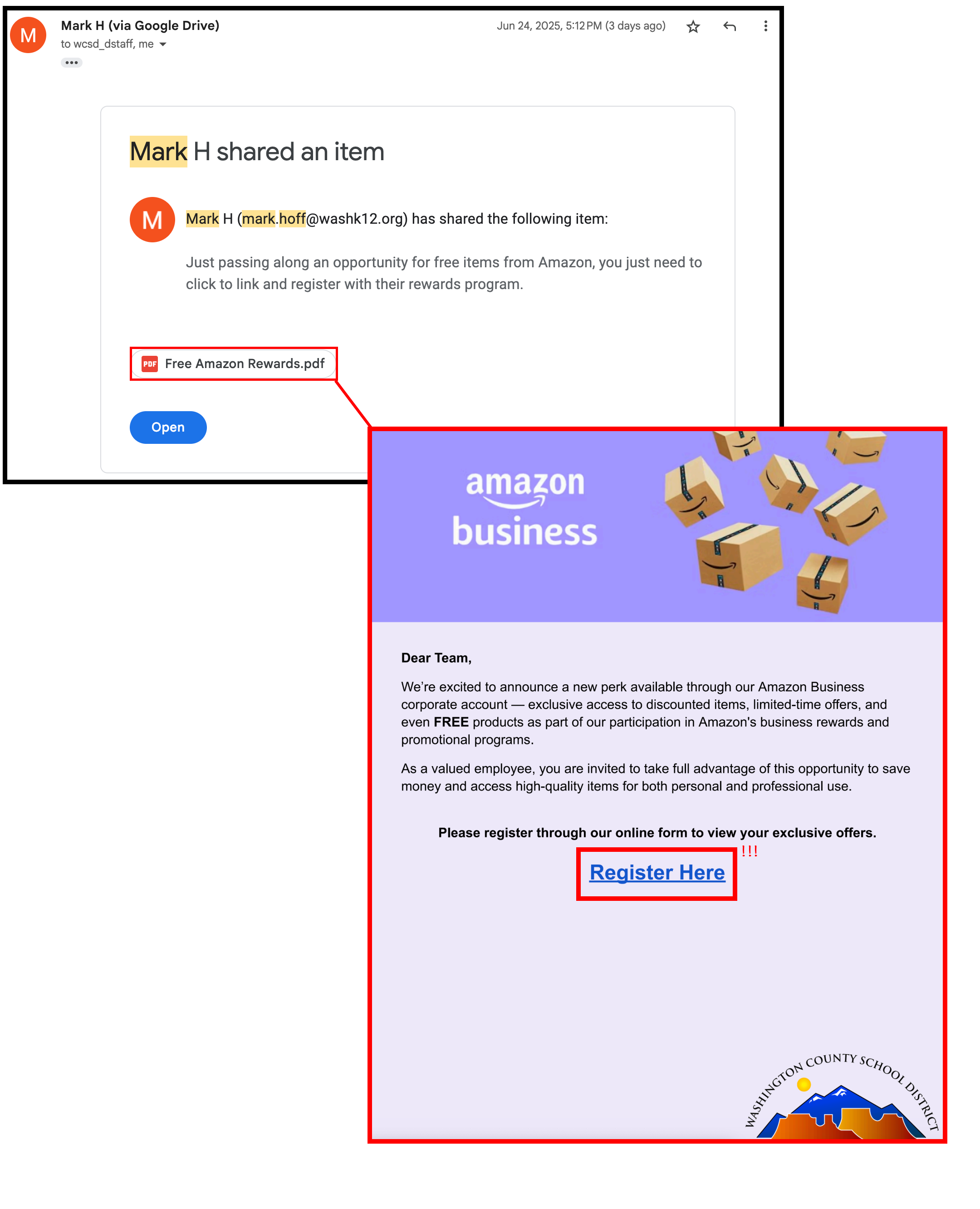
It's very important to apply a similar process that you would use when assessing internal emails.
- Be skeptical of the content: This is coming from a legitimate company, but the content of the email is suspicious and the sender is unknown.
- What does this email want? If it has a link embedded into the shared document, be extremely hesitant. PDF documents are notorious for taking you to a malicious website.
- How does it want you to respond? What information do they want to collect from you and what website is collecting it?
It is very common for a phishing email to lead you into a page impersonating the company in order to collect your account login credentials.
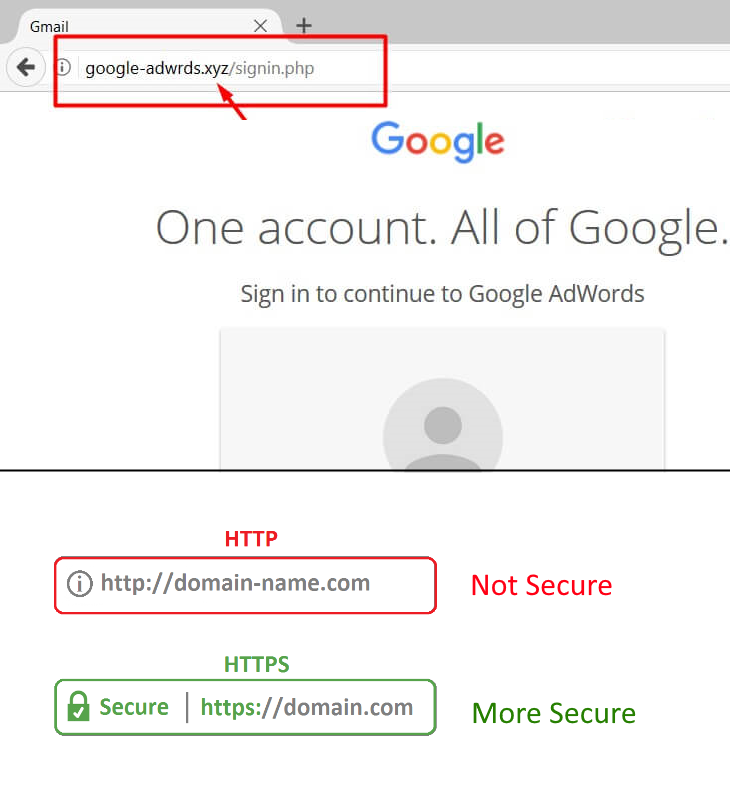
Check the full website address. Similar to checking an email address, a login page should be from a known domain for that company.
It's become a standard for modern websites to use HTTPS. This makes your connection to the site more secure and will show a lock icon in the adddress bar
Seeing the "Secure" Lock icon does not mean the site cannot be malicious, more advanced phishing pages will go through the steps to acquire a lock.
Malicious QR Codes
A QR (Quick Response) code is a type of barcode that moderm smartphones can now easily scan and read through an app or directly built into the camera. QR codes can be used for many different digital purposes such as website links, login methods, and banking transactions.

Security news outlets are steadily reporting occurences of scammers placing QR codes in public places and attempting to con victims into scanning the codes to collect their information.
What can you do? Use QR code payments only in circumstances that you consider normal, don�t be rushed or talked into paying in a way that you are not completely familiar with. Treat a QR code like any other link. Don�t follow it if you don�t know where it originated from, or if you don�t fully trust the source.
Perhaps even more annoying than spam emails are spam text messages. Ranging from actual conversations with a scammer to automated marketing links, tens of billions of scam messages are sent every year.
- Don't rely on the area code - sophisticated texts or calls will use an area code you may be famaliar with, making you more likely to respond.
- Shortened links can take you anywhere - links in text messages are typically ran through a "shortener" to shorten the length of the link. This subsequently masks the actual address of the link and you won't know where it's going until you click it. Read more about URL shorteners here
- Protect your number - In addition to placing your number on do-not-call-lists, modern phones and phone carriers offer additional ways to block, filter, and screen unknown calls to minimize your contact with scams.
The Social Security Administration urges everyone to be on the lookout for fake calls, texts, emails, websites, messages on social media, or letters in the mail regarding your Social Security Information.
- Scammers pretend to be from an agency or organization you know to gain your trust.
- Scammers say there is a problem or a prize and pressure you to act immediately.
- Scammers then tell you to pay in a specific way to fix the "issue".
Visit https://www.ssa.gov/scam/ for more information and to report a Social Security related scam.

You can forward suspicious emails to phishing@washk12.org
If you recieve any internal emails that are out of the ordinary, you can always check with them in-person!
Thank you for reading to the end!
Additional resources
(YouTube) CompTIA: 11 Tips for fake websites & phishing emails